Phishing is one of the most widespread types of fraud in the crypto industry. Its power lies in simplicity: all an attacker needs is to trick someone into clicking a link or signing a transaction. In 2023, phishing websites using wallet drainer scripts stole about $295 million from more than 320,000 wallets.
Phishing is when someone convinces you to voluntarily open the door to your wallet — by giving away your seed phrase, signing a transaction, or entering your password on a fake site.
How Phishing Works
Phishing always follows the same pattern: first, the victim is lured into a trap, then their access to assets is extracted.
1. Delivery Channels
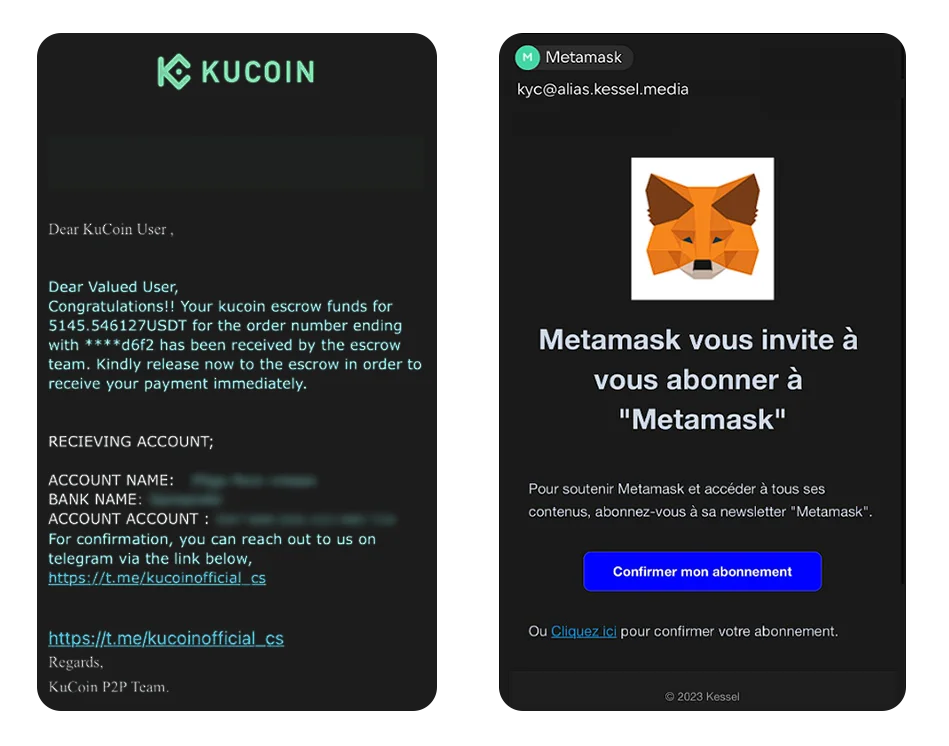
Email phishing
Emails that look like official messages from exchanges or wallets. For example, “from KuCoin” with a warning about a “security violation” or a message “from MetaMask.” More details from CISA.
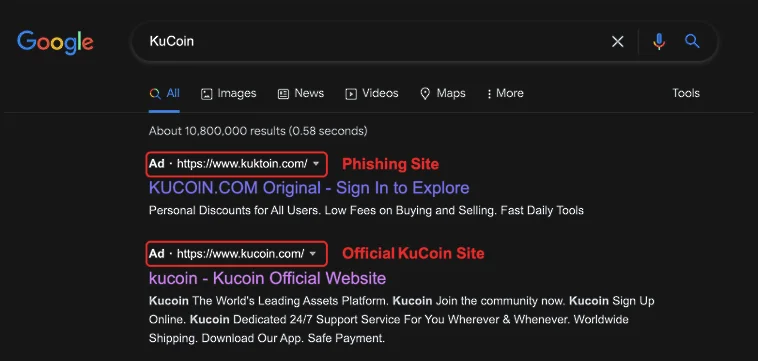
Web phishing (fake websites)
Clones of popular platforms. They often appear at the top of Google search results thanks to ads and look identical to the original. The difference may be just one character in the domain. A detailed analysis was published by ScamSniffer.
Ads and social media
Phishing links are spread through targeted ads, social media posts, or Telegram bots. For example, notcoin-airdrop.world, where victims were lured with a “free airdrop,” and wallet connection resulted in stolen funds. A similar case was MS Drainer, which stole $59M via Google Ads.

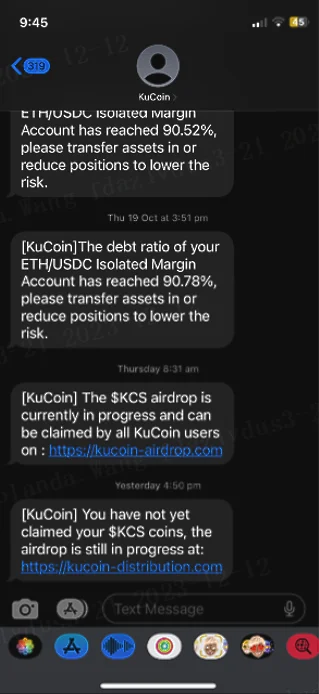
SMS phishing (smishing)
Messages “from an exchange” or “from a bank”: “Your account has been blocked, click the link.” The link leads to a fake login form.
Fake applications
Counterfeit versions of wallets like Ledger Live or Ledger’s official warning. Once installed, such apps ask for the seed phrase or steal data directly.
Communities and influencers
Fake Telegram channels, Discord groups, YouTube streams, and Twitter accounts impersonating brands or thought leaders. They promote “exclusive offers” and “giveaways.” One notorious example: Group-IB reported $1.6M stolen in just three days. This was also confirmed by BankInfoSecurity.
2. Theft Mechanics
Data theft — the victim enters a seed phrase, private key, or password into a fake form or application.
Signature phishing — the victim is persuaded to sign a transaction “to confirm security” or “to join an airdrop.” In reality, the signature gives the attacker technical permission to drain tokens.
Real Phishing Cases
$3.13M lost with one click
A user connected a wallet to a phishing site, signed a transaction — and lost $3.13M in WBTC.
More details — our Telegram breakdown.
When the hacker becomes a victim
In February 2025, a hacker stole 2,930 ETH ($5.4M) from zkLend and tried to launder it through Tornado Cash. But he ended up on a phishing clone of Tornado Cash, active for over five years. Other fraudsters took his funds.
More details — our post.
Fake apps in the App Store
In 2025, a counterfeit Ledger Live app for Mac appeared in the App Store. Users installed it, entered seed phrases, and lost funds.
YouTube streams with Musk and Buterin
In 2022, a series of fake live streams using images of Elon Musk and Vitalik Buterin brought scammers over $1.6M in just three days.
Phishing by the Numbers
According to ScamSniffer, in the first half of 2025 there were 43,628 victims who collectively lost $39.33M (average loss ~$902). Compared to H1 2024, phishing activity decreased significantly.
How to Recognize Phishing
How to Protect Yourself
