Telegram has long been known for its commitment to privacy and user anonymity, which has made it a popular platform for a wide variety of communities. However, this same openness has also attracted individuals with malicious intentions. With the growth of Pavel Durov’s broader ecosystem, particularly with the introduction of TON (The Open Network) and its technical advancements, new opportunities have arisen for cybercriminals to exploit. The ability to create mini-apps has unfortunately opened the door for more sophisticated scam activities. According to Match Systems, a leader in cryptocurrency security, these developments have accelerated the spread of fraudulent schemes in ways few anticipated. Malicious actors are increasingly taking advantage of TON’s open and decentralized structure, resulting in large-scale theft of assets and a significant challenge to user trust within the ecosystem. What was once seen as a platform for innovation is now contending with a growing wave of cyber threats. This analysis will explore the security risks associated with TON and highlight potential vulnerabilities in its expanding ecosystem.
Growing Fraud Trends in TON: The Numbers Speak
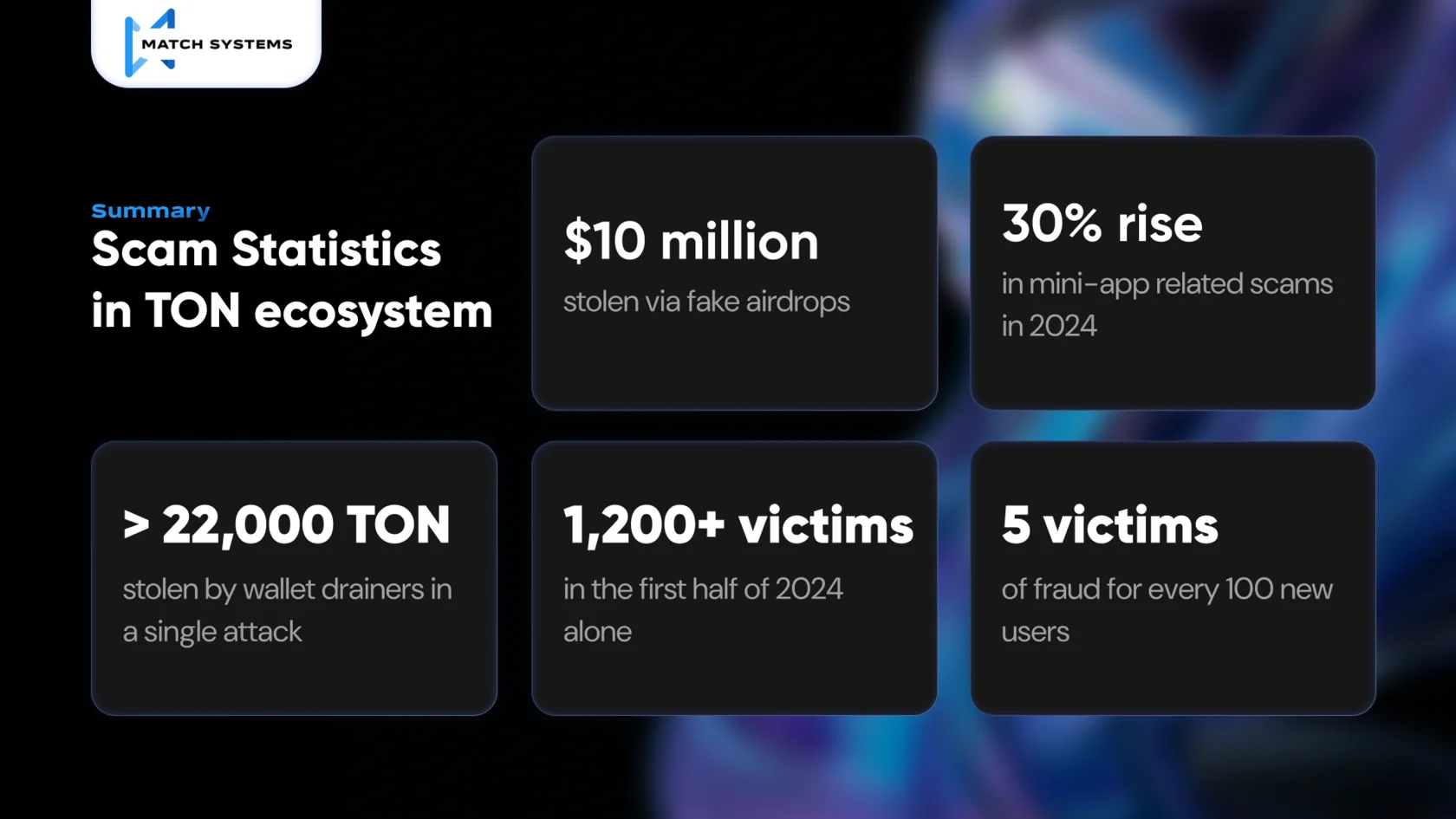
In recent years, the growth of criminal activity in the TON blockchain has raised serious concerns. The number of registered fraud cases and illegal operations has been growing exponentially. In 2023, the total number of incidents increased by 60% compared to 2022, already signaling alarm for the entire crypto community. However, 2024 brought even more shocking data: in just the first six months, over 1,200 cases of fraud were reported, which is 45% higher than the same period last year.
Particularly worrying is the monthly data. For example, in March 2024, the number of crimes in TON increased by 25% compared to February, and in June, a 30% rise was recorded, linked to the growing popularity of mini-apps on the platform. Analysts estimate that by the end of 2024, the amount of funds stolen through fraud schemes in TON could exceed $100 million, setting a new record for the ecosystem.
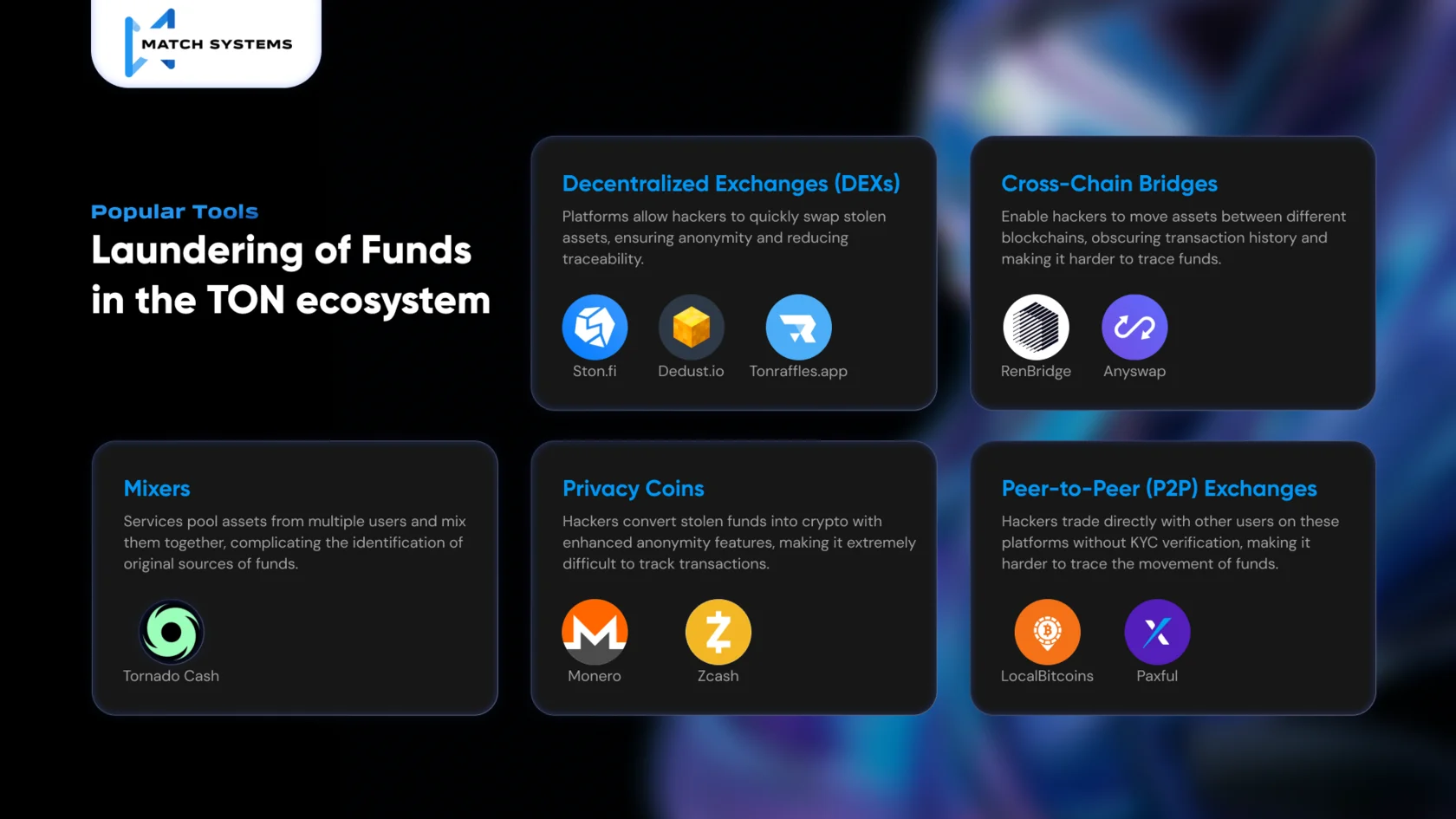
One of the most common types of fraud remains fake airdrops and phishing websites, which have already resulted in over $10 million being stolen since the beginning of 2024. Additionally, new money-laundering technologies through decentralized exchanges and mixers allow criminals to almost completely hide their tracks, complicating investigations and the recovery of stolen assets. Statistics also show that the number of fraudulent schemes in the TON blockchain is growing exponentially, with at least 5 victims of fraud for every 100 new users. This indicates a pressing need for enhanced security measures and oversight in the ecosystem, which is becoming increasingly attractive to criminals.
While Pavel Durov and the TON development team are actively working on improving the security of the ecosystem, the challenge lies in the rapid growth of the platform. With its fast-growing popularity, the development of security mechanisms hasn’t been able to keep up with the expansion of its ecosystem. However, most likely as the TON ecosystem continues to mature, it will eventually transform into a highly secure and technically advanced blockchain.
One critical issue is that many blockchain analytics platforms do not yet support TON, making it extremely difficult to track stolen assets within the ecosystem. This lack of support has left a significant gap in fraud detection, meaning that once assets are stolen within TON, they are nearly impossible to trace, further complicating recovery efforts.
Scam Schemes in TON: A New Era of Deception
In recent years, the TON ecosystem has seen a significant migration of fraudulent schemes from the Ethereum blockchain. As Ethereum continues to strengthen its security measures, with more robust wallet protections and anti-fraud tools, it is becoming increasingly difficult for scammers to operate effectively. In 2024, platforms like MetaMask and Coinbase integrated advanced security tools such as transaction simulations and warnings for suspicious activities, forcing scammers to look for more vulnerable ecosystems.
As a result, TON, with its open-source and decentralized nature, has become a prime target for these migrating scams. TON’s relatively young infrastructure and lack of widespread adoption of advanced security protocols make it attractive to fraudsters. Vulnerabilities in mini-apps, wallet systems, and smart contracts create opportunities for malicious actors. Additionally, the close integration with Telegram, which is known for its privacy features, further fuels the migration of scams. As stated by industry experts, TON “invites” scammers by offering a less secure environment compared to Ethereum.
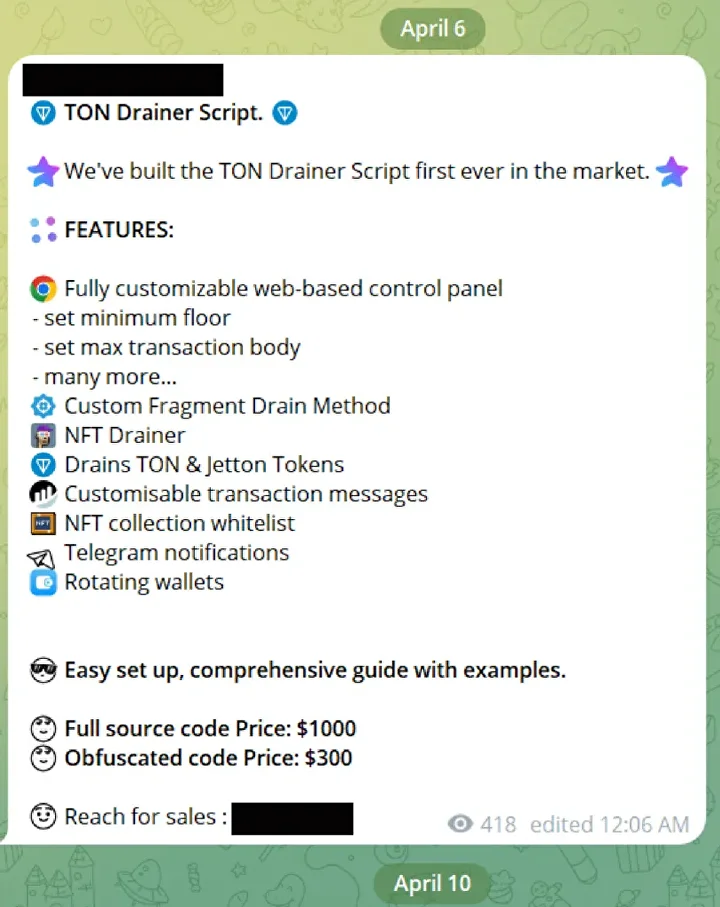
For example, wallet drainers that once targeted Ethereum are now frequently being used in the TON ecosystem. These malicious scripts exploit the weaker security measures, allowing scammers to drain users’ wallets. Drainer attacks that were blocked in Ethereum due to stronger protection are finding new life in TON, where they have resulted in significant financial losses.

Below the possible ways of scam schemes in TON ecosystem has been structured. By structuring scams this way, it becomes clearer how fraudsters manipulate both users and the technical aspects of the TON blockchain to steal assets. Each category highlights different levels of deception and exploitation, ranging from social manipulation to highly technical automated attacks.
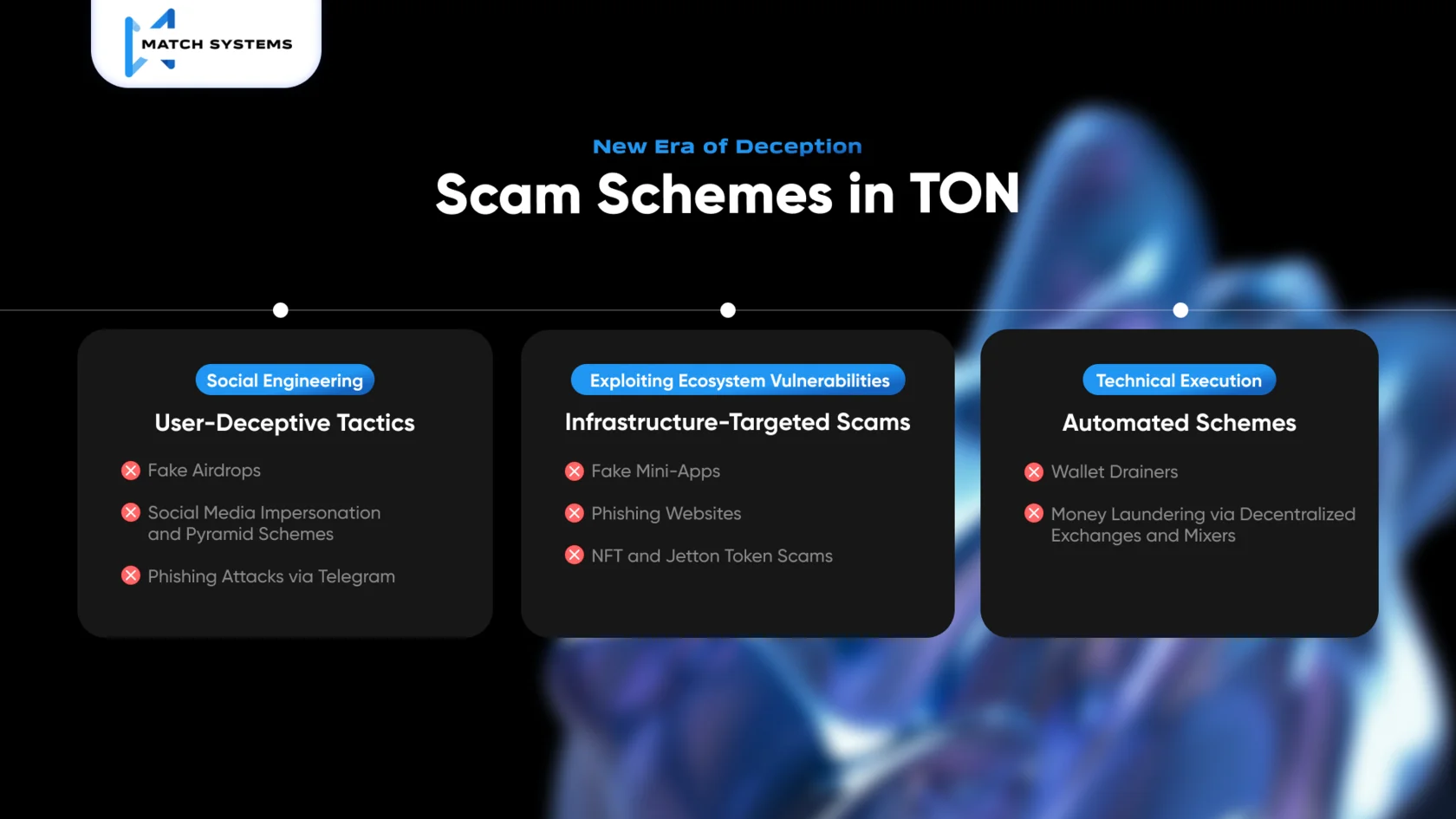
1. User-Deceptive Tactics (Social Engineering)
Scams in this category primarily rely on misleading or deceiving users into willingly surrendering their assets or sensitive information. These tactics focus on exploiting human psychology, trust, and lack of technical knowledge.
2. Infrastructure-Targeted Scams (Exploiting Ecosystem Vulnerabilities)
This category focuses on fraud that exploits weaknesses in the TON ecosystem’s infrastructure, such as apps, wallets, and smart contracts.
3. Automated Exploitative Schemes (Technical Execution)
These scams combine both technical and user deception, automating the theft process once the victim interacts with a compromised app or platform.
Popular Tools Used by Hackers to Build Infrastructure for Illegal Activity in the TON Ecosystem
In the TON ecosystem, hackers use a classical variety of services to build and maintain infrastructure for illegal activities. These services span across several key areas, including domain registration, SEO manipulation, traffic generation tools, VPNs, and proxy networks. On the infographics below is presented a detailed breakdown of the types of services typically used.
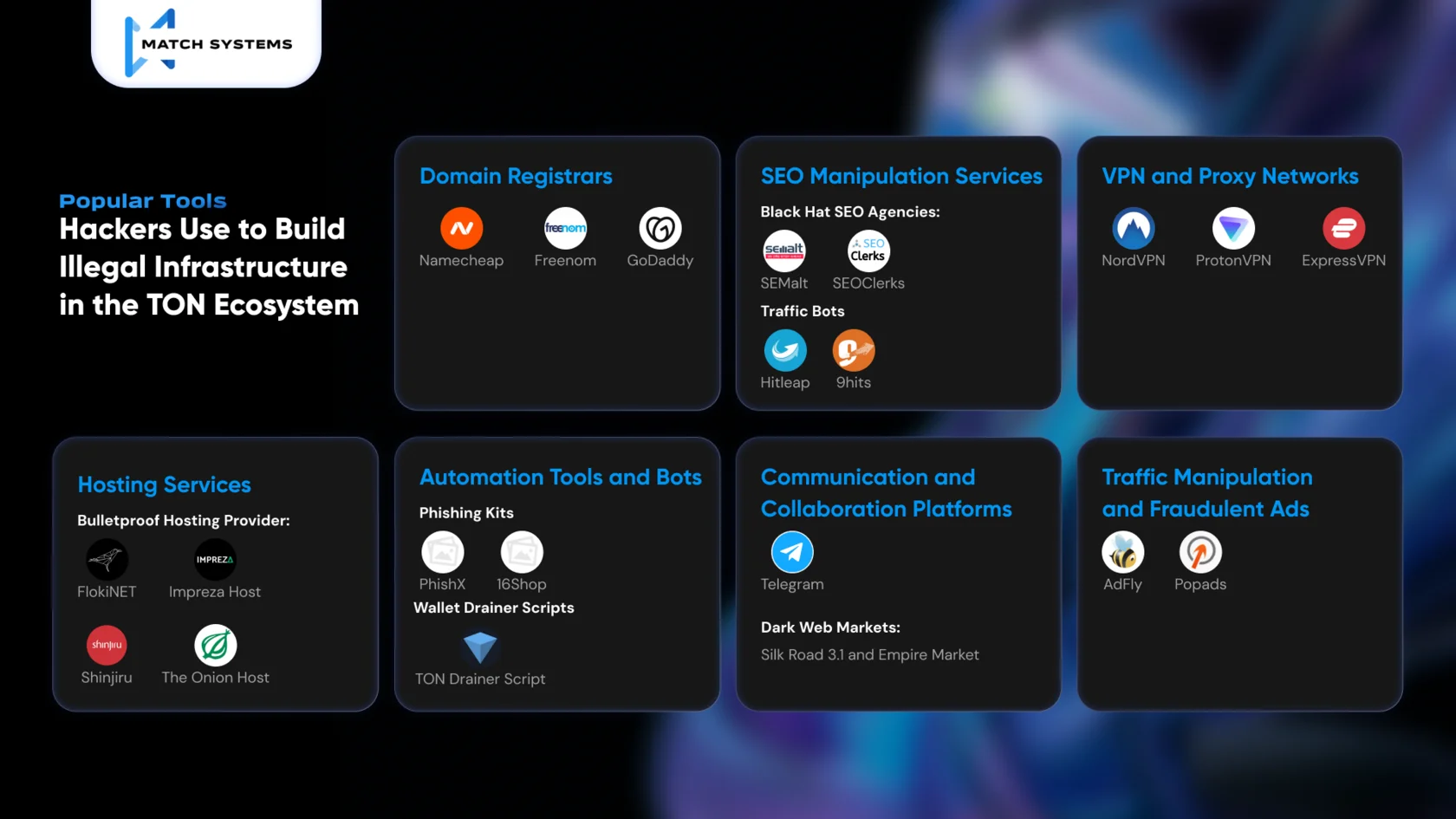
1. Domain Registrars
Examples of services used:
2. SEO Manipulation Services
Examples of services used:
3. VPN and Proxy Networks
Examples of services used:
4. Hosting Services
Examples of services used:
5. Automation Tools and Bots
Examples of services used:
6. Communication and Collaboration Platforms
7. Traffic Manipulation and Fraudulent Ads
Laundering of Funds in the TON Ecosystem tools
Checklist for Avoiding Falling Victim to Scammers
To protect yourself from scams in the TON ecosystem, Match System has prepared a simple checklist for you. By following these steps, you can significantly reduce the risk of becoming a victim of fraud in the TON ecosystem. These straightforward steps might save your money. Just follow them, and you’ll stay safe.

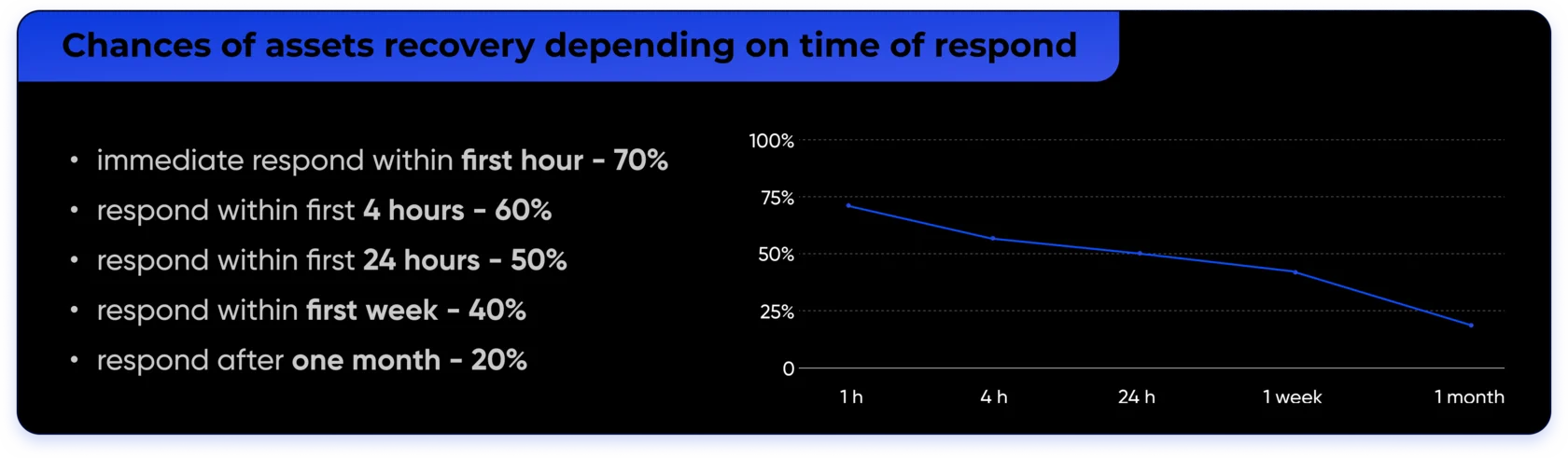
Match Systems has developed a simple tool for this purpose — the Telegram bot Report on Crypto Incident. With just a few clicks, you can report your situation. At the very least, the stolen funds will be swiftly marked in the blockchain as stolen, making it significantly harder for scammers to move them around. This process increases your chances of recovering the stolen assets.
As a conclusion
Match Systems also contributes to strengthening the security of the growing TON ecosystem. By integrating TON into its blockchain analyzer, the company enables detailed transaction tracking and identification of suspicious patterns, providing valuable support to law enforcement and financial institutions. In addition, Match Systems marks and shares fraudulent addresses with the community, helping users avoid dangerous interactions, while also offering real-time alerts on suspicious activities. Moreover, the advanced AML solutions, which include both automated and manual checks, further enhance the network’s ability to monitor and block illicit transactions.
Together, these efforts contribute to creating a safer and more secure environment for all participants in the TON blockchain ecosystem.
NB! The information provided in this article is for informational and familiarization purposes only, and the data should not be used for illegal purposes and should not be used as an inducement to act.
