Cryptocurrency has earned its place in the modern financial system. Experienced users rely on it for peer-to-peer payments, subscriptions, gaming, and online purchases. More and more people are also getting involved in projects where you can earn tokens and coins.
But the simplicity and convenience of crypto come with serious risks. People constantly lose access to their wallets, get scammed out of significant sums, and are left asking the same desperate question: what do I do now?
Recovering stolen cryptocurrency on your own is virtually impossible today. The schemes used by attackers have grown sophisticated enough that professional help is almost always necessary.
In this article, we break down the most common attack and fraud methods used in the crypto industry. Ais Dorzhinov, Co-Founder of Match Systems, shares advice on how to minimize losses — and what to do if you’ve already been hit.
How Do Crypto Attackers Operate?
Major specialized firms that handle fraud incidents and crypto investigations typically build their own analytics on the methods currently in use. Match Systems analyzed incidents from 2025 and identified the most prevalent schemes.
Crypto Drainers
A crypto drainer is a type of malicious software designed to instantly and automatically access a crypto wallet and drain all its assets. A drainer isn’t a standalone scam — it’s the mechanism behind many others. Nothing is “hacked” in the traditional sense. Instead, you’re pressured into connecting your wallet and signing permissions yourself. The script does the rest.
Drainers are typically disguised as innocent-looking websites and links. They come in several forms:
Phishing Sites
Phishing is a fraudulent scheme where attackers impersonate legitimate, trusted crypto services or exchanges. Users who land on a fake service page enter their credentials or private keys — and that sensitive information goes straight to the attacker. Links to these pages are often distributed through ad banners, social media posts, or spoofed emails.
On-chain investigator ZachXBT recently reported the compromise of a major investor’s wallet, resulting in a loss of over $55 million in DAI stablecoin. The attack used a well-known phishing tool called Inferno Drainer.
For a full breakdown of phishing mechanics, real-world cases, and protection strategies, see our dedicated guide: Crypto Phishing: The Complete Guide

Fake AML Checks
A particularly widespread variant of phishing involves impersonating a wallet “cleanliness” check. Scammers offer to verify the origin of your assets — especially in the context of P2P trades or buying USDT at an attractive rate. You’re directed to a phishing site that perfectly mimics a well-known AML service, where you’re asked to connect your wallet “for verification.” The moment you connect and sign the permission, funds are swept instantly.
One thing to understand clearly: a real AML check never requires wallet connection. AML analysis is about reviewing an address, not accessing your assets. If a site asks you to connect your wallet and you weren’t planning a DeFi transaction — close the tab.
Malware
Scammers distribute specialized software that installs silently on users’ devices and PCs — then remotely logs keystrokes, takes screenshots, or intercepts crypto wallet login data. These programs spread through fake applications, links to untrusted sites, or infected files.
In 2024, Chinese hackers launched a scheme involving fake Skype and WhatsApp apps with built-in malware. Once installed, the software gave attackers access to device data — and automatically replaced any TRON or Ethereum addresses found in messages with the attackers’ own.
Clipboard Hijacking
One of the most basic yet effective methods. Malware monitors your clipboard: the moment you copy a recipient’s address, it silently replaces it with the attacker’s address. The switch is hard to spot visually, since the first and last characters of the fraudulent address are often identical to the original.
How to stay safe: Always verify at least the first and last 6–8 characters of an address before sending. For large amounts, verify the full address. A hardware wallet displays the final destination address independently of your computer’s state.
Fake Wallets and Browser Extensions
Scammers create fake apps or browser extensions that mimic legitimate crypto wallets. Once installed, they request private keys or seed phrases. In 2024, a fake WalletConnect scheme was particularly popular: users received notifications about “account issues,” and links in the emails led to phishing pages.
Match Systems recommendations:
P2P Transactions and Legal Risks
This is a growing concern: the risks embedded in ordinary P2P transactions, even ones that appear entirely unrelated to fraud.
Here’s how the scheme works: you sell USDT through a P2P platform, and the money arrives in your bank account. Later, it turns out the payment came from a fraud victim — a third party, not your actual counterparty. The crypto went to the scammer, but the victim’s complaint and the resulting criminal investigation land at your door. The risk here isn’t just losing funds — it’s becoming a party to a criminal case. According to the FBI, crypto fraud victims in the US lost more than $5.6 billion in 2024.
How to reduce risk:
Exchange and Platform Hacks
Major crypto exchanges and platforms are frequently targeted through social engineering — manipulative conversations and phone calls from fake identities. Exchange employees are often the primary targets.
In a successful breach, attackers can obtain:
In July 2024, India’s largest crypto exchange, WazirX, was hacked — attackers withdrew more than $235 million in various cryptocurrencies.
OTC Traps
An acquaintance reaches out asking you to help their “contact” exchange a large sum of crypto. You’re sent “proof”: wallet balance screenshots, screen recordings, sometimes notarized documents. The screenshots typically show older wallet versions (like Electrum or Mycelium) that allow any public address to be imported in watch-only mode — the balance displays, but no private keys exist. You’re being shown a display, not proof of control.
If you take the bait, phase two begins: pressure to connect your wallet to a phishing site or sign a transaction “for verification.”
The key rule: don’t get involved in “large sum via acquaintance” schemes. Always require a test transaction from the address where the funds are supposedly held — that’s the only way to verify actual control over the assets.
Fake Investment Platforms
The mechanics of fake investment platforms are straightforward. Through aggressive spam, they promise high returns and lure in trusting “investors” — then vanish with the deposited funds.
Match Systems: how to tell a real investment platform from a fake one:
In 2024, Indian police shut down the fraudulent platform GBE Crypto Trading Company — funds were being siphoned through a fake app promoted via Telegram and WhatsApp.
Pig Butchering
This is a long-con scam built entirely on trust: romantic connections, friendships, professional relationships, “investment clubs” in messaging apps. The scammer carefully cultivates a personal relationship — a process that can take weeks or months — before convincing the victim to invest a significant sum on a fictitious platform.

The classic playbook:
How to reduce risk: Verify any platform through independent sources and OSINT. It should have a license, a public track record, and reviews on independent sites. Any doubt is a red flag.
Pig butchering is one of the most technically complex and psychologically damaging scams in existence. We’ve dedicated a full breakdown to it: Pig Butchering: How Trust-Based Fraud Works
Dust Attacks
A microscopic amount of cryptocurrency — “dust” — arrives at your address. The amount has no economic value, but the attack does. A dust attack isn’t direct theft; it’s reconnaissance or preparation for the next stage.
The main variants:
How to reduce risk: Simply ignore the dust. Never copy an address from your transaction history — only use addresses you’ve saved yourself. Don’t interact with unknown tokens.
The “Leaked” Seed Phrase Scheme
A seed phrase gets “accidentally” posted publicly, or a message appears: “I’ve got 3,000 USDT sitting here. Don’t need it — take it.” You check — the tokens are really there. Only there’s no native coin for gas fees. Just a couple of dollars needed.
These wallets are controlled by bots: the moment any native coin arrives to cover fees, it’s swept instantly. The tokens themselves may be locked by a smart contract or otherwise inaccessible without the bot owner’s involvement. The takeaway is simple: free 3,000 USDT doesn’t exist.
Ponzi Schemes
A special category of fraud in which “investors” are promised high returns funded by money from an ever-growing pool of new participants.
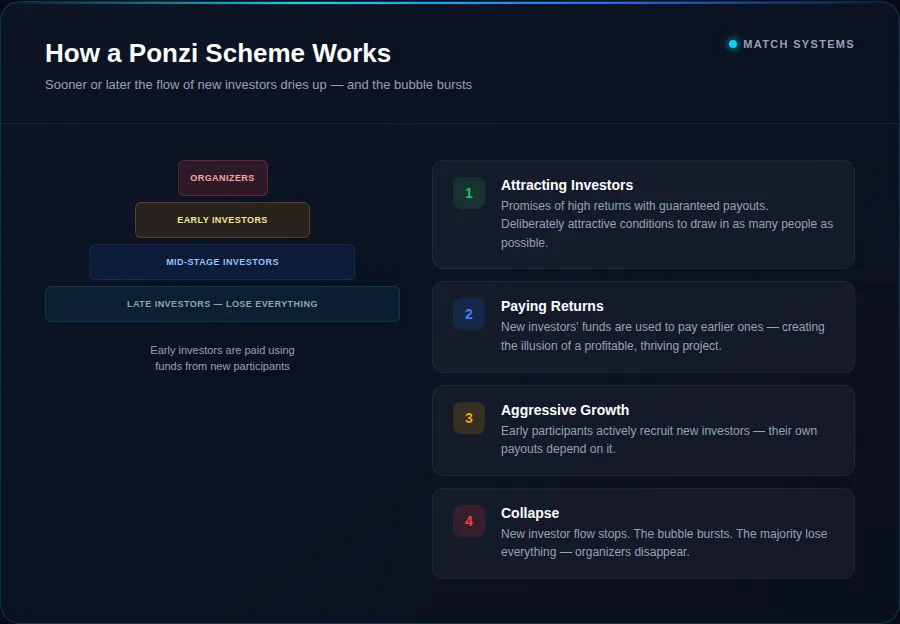
How a crypto Ponzi works:
One of the most notorious examples in crypto history is BitConnect. In 2018, the SEC shut down the project on fraud charges — by that point it had raised more than $2.5 billion.
Fake Token Sales and ICOs
Fraudulent projects raise funds under promises of innovative technology and high-return investments — then simply vanish. One example is Centra Tech: in 2017 the project raised $25 million through an ICO, after which the founders were arrested for fraud and exchanges delisted the CTR token.
Recovery Scams
This is the second wave of fraud — the one almost no one warns you about in advance.
You’ve already been robbed. You’re shaken. And then someone appears with an offer: “We work with blockchain analysts and law enforcement. We’ll recover your funds for 10–20%.” This is a calculated exploit of the shock state — victims feel the need to act immediately.
They show you blockchain transactions, convincing “analyst” reports, correspondence with “law enforcement officers.” Then they ask for a significant upfront payment. If you keep engaging, pressure mounts — promises of fast recovery paired with threats of “even bigger problems” if you go to the police.
Red flags — stop the conversation immediately if:
We’ve broken this scheme down in detail — how to recognize it and why victims end up losing their money twice: Recovery Scams: The Complete Guide
SIM Swapping
Attackers reissue your SIM card through a bribed carrier employee, take control of your phone number, and intercept SMS verification codes. If an exchange, email account, or 2FA is tied to that number — the account can be seized.
This is exactly how American entrepreneur Michael Terpin was attacked: despite additional security measures, criminals stole $24 million in digital assets.
How to protect yourself:
How to Protect Your Crypto Assets

Cyber Hygiene for Crypto Wallet Users

Documenting a Theft: What You’ll Need When Contacting Law Enforcement
The main obstacle for most victims in recovering stolen crypto is not knowing how to document the theft properly. To open a criminal case, you need solid evidence.
You will need:
How to Recover Stolen Cryptocurrency
Tracing the Transactions
Use blockchain explorers: blockchain.com for Bitcoin, etherscan.io for Ethereum. If you manage to trace the stolen crypto to an exchange — contact their team immediately and request that the address be flagged and frozen.
Contacting the Right Organizations
In many countries, dedicated law enforcement units for crypto crime are still forming or don’t yet exist. To open a case, you can file with local police or specialized cybercrime units — the FBI’s IC3 in the US, Action Fraud in the UK, BKA in Germany. In parallel, consider reaching out to private firms that specialize in investigation and legal support for these cases. Match Systems is one such company.
For a step-by-step guide on what to do immediately after a theft, see our detailed resource: How to Recover Stolen Cryptocurrency
How Match Systems Helps Recover Cryptocurrency
Telegram bot: @ms_main_bot
Through the bot you can: report an incident, receive a free step-by-step action plan, place a “tracker” on the stolen crypto chain with movement notifications, request an analytical report on the transactions, and obtain a template for filing a report with law enforcement.
Match Systems specialists:
Key Takeaways
The risk of having your crypto stolen shouldn’t be underestimated — it can happen to anyone. But in crypto there’s no customer support hotline, and there’s no disputing a transaction. Responsibility is personal, and transactions are final.
Three principles that work better than any promise:
Slow down. Urgency is a scammer’s favorite weapon.
Separate. Wallets, roles, devices. Keep your holdings separate from your operational wallet.
Keep quiet. The fewer people who know about your assets, the smaller your target profile — online and offline.
Trying to investigate on your own without specialized knowledge will most likely yield nothing — and cost you precious time. It’s always better to go straight to professionals who handle blockchain investigations for a living. Fast, coordinated action often makes full recovery possible.
