More than 1,500 bitcoins (more than 100 million US dollars at the current rate), which had been stored in hackers stashes for more than 7 months, began to move. Stolen Funds that are associated with major hacks in recent years, and previously attributed by the FBI Investigation to the activities of the Lazarus Group (FBI Press Release), began to laundering.
Here is a list of these addresses:
3LU8wRu4ZnXP4UM8Yo6kkTiGHM9BubgyiG
39idqitN9tYNmq3wYanwg3MitFB5TZCjWu
3AAUBbKJorvNhEUFhKnep9YTwmZECxE4Nk
3PjNaSeP8GzLjGeu51JR19Q2Lu8W2Te9oc
3NbdrezMzAVVfXv5MTQJn4hWqKhYCTCJoB
34VXKa5upLWVYMXmgid6bFM4BaQXHxSUoL
Our team of analysts, which is investigating this incident, determined that to date, hackers have already managed to launder more than 44 BTC (more than $3m at current rate) through cryptocurrency exchanges HTX, CoinEx and FixedFloat.
Despite the presence of sanctions markings, hackers almost freely manage to launder stolen funds through cryptocurrency exchanges that comply with AML policies. This is largely possible due to fact that hackers use special laundering schemes that allow them to mislead AML systems of exchanges, which do not always keep up with markings and learn about acceptance of stolen funds after hackers already withdraw them from exchanges.
Match Systems urges cryptocurrency exchanges and the whole crypto community to pay attention to above hacker addresses in order to prevent hackers from carrying out their plans.
Hacker:
Safemoon team:
Key Events Timeline
The chronology of the incident (UTC) as is

Our Zoo
The points of interests, as of above:

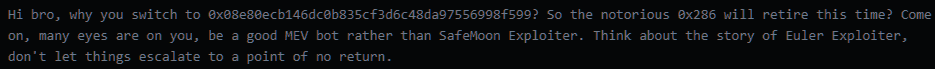
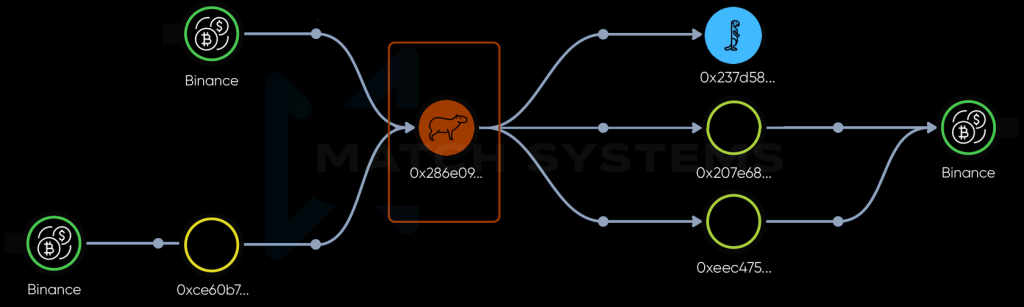
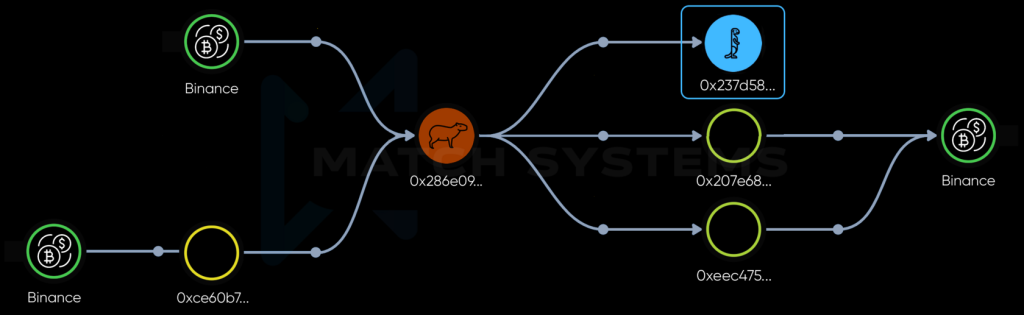
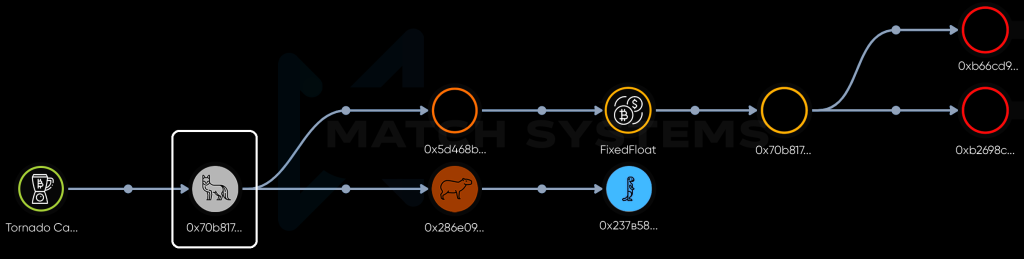
0x286e09932b8d096cba3423d12965042736b8f850 – the address of the initial withdrawal of assets from the smart contract. Also used by hacker to message Safemoon project team (we will call it “Red-haired Capybara“)

0x237d58596f72c752a6565858589348d0fce622ed – the address where the assets are currently held. (we’ll call it “Blue meerkat“) 000000000000000000000000000000

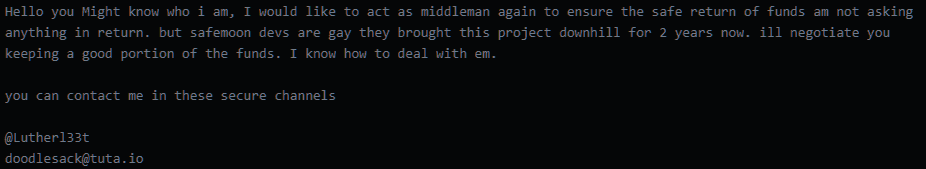
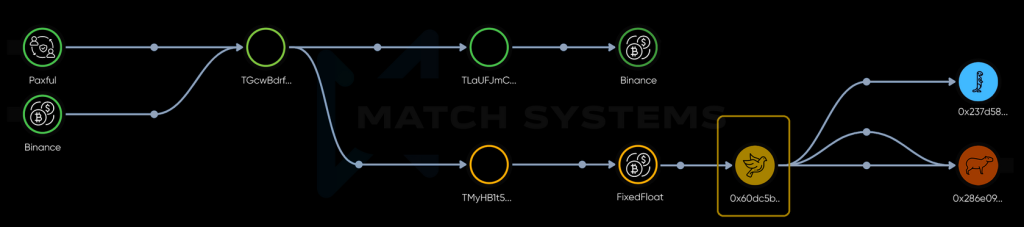
0x60dc5bb048310224b8732d732f4a32d16690e470 – the address from where the message offering the mediator for negotiations was received (let’s call it “Yellow Pigeon“)

0x60dc5bb048310224b8732d732f4a32d16690e470 – the address from where the message offering the mediator for negotiations was received (let’s call it “Yellow Pigeon“)
De-anonymization of the beasts
0x207e689ba4fdcd8e6e3a4a40d8247d7cce1462b3, 0xeec475b4bed5822eef6ccda45c52ff54da1414f7
and the transaction initiators who supplied with “gas”
0x34927071e8c58c99db192b88f58a3ef2b1b6cf998f21dc1a08be270e519ec57e
0xb730a8be2a0a2ec13aba48fcc33dae8a1d5e31383df270fee16d48b681e1c861
0x40e2969e2c88c642a332acaca8c706d3c415d8a253d45d36ca77c6b6a790d54f
0x1ee79a12b795d3554e98c4c84c482f2e2f3b6eb87e80649dfccee20f8e818382
0x24da81ed18e1d129dffdbb9ffa0c8c37edfd22b012f52d89030a45169f47a17e
TLaUFJmCwU3GazcmHKVkvNKE4EgU9qmvYH
and the transaction initiator who supplied with “gas”
2b081cd589254db6ed7eaf5128d2a3c762ac66bea183d4ce2a65941279984fa8
Also from Paxful about other initiatiors:
656995b7d2af3941f916db96cbd1d903717ca869b877b37042bef7e2503cc4c5
036ca0e667922e741d3813666bc04bb76f8b34f3c875d72ca5f8f82ba91b9c45
b6e2ff66ee8e6f28476a6d02a5cb9c439546fee306f4ee589e1ea30ba43cc1b9
3fc3ab6748937ddd9d791c036673b7cf90f55b71cb64bddebe76b0d5b4edda0c
Some Hack technical details and the community response
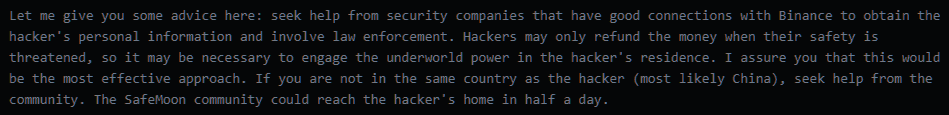
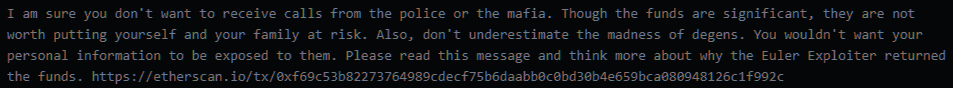
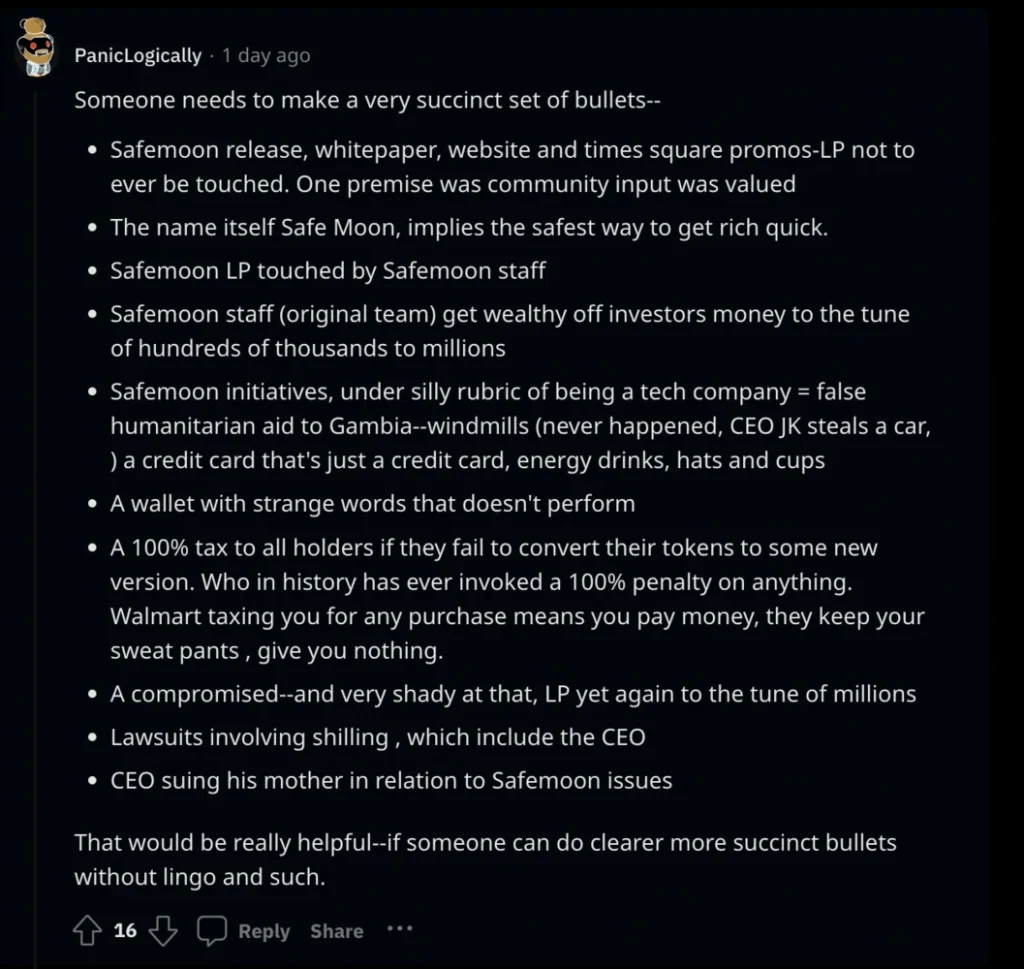
This bug, in turn, has caused a wave of outrage and accusations against the developers. The community denied the idea that this bug was accidental and accused the developers of intentional bug implementation into a functioning smart contract.
More, and more, and more…
Among other things, the user of “https://dune.com/” with nickname “@factsudeny” published the addresses which, in his opinion, were related to Safemoon and provided analysis for those addresses. Cross-chain analytics shows that these addresses have matches in various 0x blockchains, but until it’s confirmed they belong to Safemoon and the need to study them at all is established, further research is out of interest.

In lieu of a conclusion
The study found close ties between attackers and centralized cryptocurrency exchanges, which, in turn, will allow law enforcement agencies to request relevant data and identify the individuals involved, if there is an unbiased reason to do so
The fact that the developers made changes to the smart contract that allow such manipulations deserves additional attention. Considering that the previous version of the smart contract did not have such vulnerabilities, and after the update, a hack occurred in a relatively short period – it seems reasonable to conduct an additional internal audit regarding the individuals involved in making these changes.
Postscriptum
This research may be incomplete and some information may be missing because it was done by our team own time for practice purposes. At the time of writing, we do not have any contract or NDA restricting us to collect, analyse or spread the information, as well as in depth research of the incident, if necessary.
